There has been a lot of chatter lately about two-factor identification and the need to supplement the time honored password and "secret question" approach. The primary method being discussed is the use of individual authentication by text message via SMS (Short Message Service). When you sign on to a site, say Facebook, you receive an authentication code by SMS and you then enter that code and you are signed in. The problem is that in order to use this system, you have to supply your mobile phone number. And this is when the brick comes out of the wall. Two things happen as you accept the premise of this two-factor approach. The site has your number for data mining use, and hackers have more detail than ever to retrieve. Once they have access to your Facebook account, Google Docs, or whatever the site may be, they can learn a lot about you very quickly.
Well, you may say, "the cell phone is encrypted and I am protected from hackers". Another brick falls out. Why? Let me tell you a story that illustrates why I am concerned about cell phone and WIFI systems.
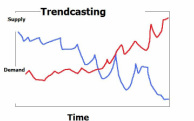
Several years ago I began following the underground hackers and particularly, the war-driving sites. These are the people who drive around searching for unencrypted and accessible WIFI and cell phone activity. They can then "jump on" and use the bandwidth connection, or read the data on the computer or phone. At that time, the hardware and software were fairly difficult to use but were effective. And the software was free, and as free as the password crackers are now. But that has all changed and both the hardware and software are easy to use and can be downloaded by any potential hacker. And, I am certain that they would really like to do their holiday shopping on your dime. The trend? It will become easier to steal information and hack into your information. As I have posted before, when you enter the internet, you are doing so at your own risk. Even a biometric approach like a fingerprint can be hacked.
There are some preventive measures that can reduce vulnerability, but can not guarantee anything. First, use a complex pass word and not one that is easy to remember. Simple passwords just makes it easier to hack. Second, keep your mobile phone number to yourself and other "real people" that you trust. And third, cross your fingers!
 RSS Feed
RSS Feed
